Deceptive language frequently used against consumers: Difference between revisions
Fixed a few tone issues and added citations |
|||
| Line 14: | Line 14: | ||
<blockquote> | <blockquote> | ||
Google says you should think of the new requirements like checking IDs at the airport. | Google says you should think of the new requirements like checking IDs at the airport. | ||
</blockquote> | </blockquote>Critics argued the comparison was misleading, noting that airlines own their aircraft, while consumers own their smartphones. <ref>{{Cite web |last=Sohn |first=Jiyoung |date=2026-03-23 |title=Ads Are Popping Up on the Fridge and It Isn’t Going Over Well |url=https://www.wsj.com/lifestyle/samsung-refrigerator-ads-lg-whirlpool-ge-10ea7bcc |url-status=live |archive-url=https://web.archive.org/web/20260326132248/https://www.wsj.com/lifestyle/samsung-refrigerator-ads-lg-whirlpool-ge-10ea7bcc |archive-date=2026-03-23 |access-date=2026-04-09 |website=The Wall Street Journal}}</ref> | ||
===Storage access restrictions in Android=== | ===Storage access restrictions in Android=== | ||
| Line 23: | Line 23: | ||
</blockquote> | </blockquote> | ||
In practice, Storage Access Framework's main restriction is preventing apps from accessing the root directory of external storage. | |||
Storage Access Framework is no replacement for legacy storage access given its slowness from its large processing overhead. The performance loss may be concealed to some extent from the fast hardware smartphones have nowadays, but even then, it increases battery usage. In addition, it breached compatibility with all apps previously developed over the span of several years.<ref name="SAF">[https://www.xda-developers.com/android-q-storage-access-framework-scoped-storage/ The Storage Access Framework is the only way for apps to work with all your files in Android Q. And it's terrible.] - XDA developers ([https://web.archive.org/web/20260222042955/https://www.xda-developers.com/android-q-storage-access-framework-scoped-storage/ Archived])</ref><ref name=":0">{{Cite web |date=14 Apr 2017 |title=Horrible access storage framework performance |url=https://old.reddit.com/r/androiddev/comments/65dn8x/horrible_access_storage_framework_performance/ |archive-url=https://web.archive.org/web/20250823190730/https://old.reddit.com/r/androiddev/comments/65dn8x/horrible_access_storage_framework_performance/ |archive-date=23 Aug 2025 |website=[[Reddit]] - r/androiddev}}</ref> | Storage Access Framework is no replacement for legacy storage access given its slowness from its large processing overhead. The performance loss may be concealed to some extent from the fast hardware smartphones have nowadays, but even then, it increases battery usage. In addition, it breached compatibility with all apps previously developed over the span of several years.<ref name="SAF">[https://www.xda-developers.com/android-q-storage-access-framework-scoped-storage/ The Storage Access Framework is the only way for apps to work with all your files in Android Q. And it's terrible.] - XDA developers ([https://web.archive.org/web/20260222042955/https://www.xda-developers.com/android-q-storage-access-framework-scoped-storage/ Archived])</ref><ref name=":0">{{Cite web |date=14 Apr 2017 |title=Horrible access storage framework performance |url=https://old.reddit.com/r/androiddev/comments/65dn8x/horrible_access_storage_framework_performance/ |archive-url=https://web.archive.org/web/20250823190730/https://old.reddit.com/r/androiddev/comments/65dn8x/horrible_access_storage_framework_performance/ |archive-date=23 Aug 2025 |website=[[Reddit]] - r/androiddev}}</ref> | ||
===Non-replaceable batteries since the Samsung Galaxy S6=== | ===Non-replaceable batteries since the Samsung Galaxy S6=== | ||
Justin Denison, Samsung's public relations person, said:<ref>[https://www.youtube.com/watch?v=U8mfEud8n4c Samsung Galaxy Unpacked 2015 - Livestream (Replay] ([https://preservetube.com/watch?v=U8mfEud8n4c Archived])</ref> | Justin Denison, Samsung's public relations person, said:<ref name=":1">[https://www.youtube.com/watch?v=U8mfEud8n4c Samsung Galaxy Unpacked 2015 - Livestream (Replay] ([https://preservetube.com/watch?v=U8mfEud8n4c Archived])</ref> | ||
<blockquote>We refused to do this for some time. That's because we didn't want to have a built-in battery, until we were absolutely sure that users would feel confident about charging their phones. </blockquote> | <blockquote>We refused to do this for some time. That's because we didn't want to have a built-in battery, until we were absolutely sure that users would feel confident about charging their phones. </blockquote> | ||
| Line 34: | Line 34: | ||
The OnePlus Pad has a serialized battery, meaning the device detects repairs not approved by OnePlus, which can result in functionality being disabled. This is an anti-repair practice first seen on Apple iPhone 11. | The OnePlus Pad has a serialized battery, meaning the device detects repairs not approved by OnePlus, which can result in functionality being disabled. This is an anti-repair practice first seen on Apple iPhone 11. | ||
OnePlus used the term "encryption" to describe this battery serialization. Critics noted that "encryption" carries positive associations unrelated to its use here, and that the term obscures the restriction's effect on independent repair.<ref>{{Cite web |last=Rossmann |first=Louis |date=2023-02-08 |title=Oneplus' tablet uses an encrypted battery; how's that for repairability? |url=https://www.youtube.com/watch?v=UgtFSHCGNIk |access-date=2025-10-01 |website=YouTube |type=Video |url-status=live |archive-url=https://preservetube.com/watch?v=UgtFSHCGNIk |archive-date=16 Feb 2026}}</ref><ref>{{Cite news |last=Amadeo |first=Ron |date=2023-02-07 |title=OnePlus takes on the iPad with the OnePlus Pad |url=https://arstechnica.com/gadgets/2023/02/oneplus-takes-on-the-ipad-with-the-oneplus-pad/ |access-date=2025-10-01 |work=Ars Technica |url-status=live |archive-url=http://web.archive.org/web/20251118200050/https://arstechnica.com/gadgets/2023/02/oneplus-takes-on-the-ipad-with-the-oneplus-pad/ |archive-date=18 Nov 2025}}</ref> | |||
==="Web Environment Integrity API" by Google=== | ==="Web Environment Integrity API" by Google=== | ||
Google tried to implement [[Digital rights management|Digital | Google tried to implement [[Digital rights management|Digital Rights Management]] (DRM) on the Internet, giving it the name "Web Environment Integrity API".<ref>[https://www.youtube.com/watch?v=0i0Ho-x7s_U Google's trying to DRM the internet, and we have to make sure they fail] - Louis Rossmann ([https://www.brighteon.com/1f4125e9-f0cd-46a3-bf38-0ff22881c0f9 Brighteon mirror], [https://old.bitchute.com/video/Jl7ze8KjhWvK/ BitChute mirror]) ([https://preservetube.com/watch?v=0i0Ho-x7s_U Archived])</ref><ref>{{Cite web |last=Bruchon |first=Jody |date=2023-07-22 |title=Web Environment Integrity Must Be Stopped: Enslavement By "Remote Attestation" |url=https://www.jodybruchon.com/2023/07/22/web-environment-integrity-must-be-stopped-enslavement-by-remote-attestation/ |access-date=2025-10-01 |website=jodybruchon.com |url-status=live |archive-url=http://web.archive.org/web/20251201031758/https://www.jodybruchon.com/2023/07/22/web-environment-integrity-must-be-stopped-enslavement-by-remote-attestation/ |archive-date=1 Dec 2025}}</ref> | ||
=="To enhance our services"== | =="To enhance our services"== | ||
| Line 50: | Line 50: | ||
</blockquote> | </blockquote> | ||
Despite using benevolent-seeming phrases such as "enhance our service" and " offer additional content", the | Despite using benevolent-seeming phrases such as "enhance our service" and " offer additional content", the update introduced advertisements on the refrigerator's display.<ref name=":1" /> | ||
=="To streamline the experience"== | =="To streamline the experience"== | ||
| Line 68: | Line 68: | ||
Google restored write access in Android 5.0 through the Storage Access Framework. However, the framework introduces processing overhead that reduces speeds, particularly when handling large numbers of files.<ref name="SAF" /><ref name=":0" /> | |||
==References== | ==References== | ||
Revision as of 03:37, 9 April 2026
⚠️ Article status notice: This article has been marked as incomplete
This article needs additional work for its sourcing and verifiability to meet the wiki's Content Guidelines and be in line with our Mission Statement for comprehensive coverage of consumer protection issues. In particular:
- Tone issues
This notice will be removed once the issue/s highlighted above have been addressed and sufficient documentation has been added to establish the systemic nature of these issues. Once you believe the article is ready to have its notice removed, please visit the Moderator's noticeboard, or the discord and post to the #appeals channel.
Learn more ▼
Deceptive language used by companies to impede the rights of consumers while appearing benevolent comes in many forms. Many of them can be boiled down to a few principles.
"For the safety of the consumer"
This is one of the most cited reasons to restrict what a consumer is allowed to do with their property. It is used to fight against right-to-repair legislation, restrict downloading of apps unless provided by Google or Apple, etc. Some notable incidents include:
Google comparing APK restrictions to airport security
For many years, one of the primary selling points of Android smartphones was that no big corporation could gatekeep what the user can run on their phones. But starting with Android 17 in 2026, only developers manually approved by Google can create APKs that install on Android.
Developers applying for approval are required to violate their privacy by disclosing their real-life identity to Google.
Google used false benevolence to excuse this restriction:[1]
Google says you should think of the new requirements like checking IDs at the airport.
Critics argued the comparison was misleading, noting that airlines own their aircraft, while consumers own their smartphones. [2]
Storage access restrictions in Android
From source.android.com:
Third-party apps must go through the Storage Access Framework to interact with files on portable storage; direct access is explicitly blocked for privacy and security reasons.
In practice, Storage Access Framework's main restriction is preventing apps from accessing the root directory of external storage.
Storage Access Framework is no replacement for legacy storage access given its slowness from its large processing overhead. The performance loss may be concealed to some extent from the fast hardware smartphones have nowadays, but even then, it increases battery usage. In addition, it breached compatibility with all apps previously developed over the span of several years.[3][4]
Non-replaceable batteries since the Samsung Galaxy S6
Justin Denison, Samsung's public relations person, said:[5]
We refused to do this for some time. That's because we didn't want to have a built-in battery, until we were absolutely sure that users would feel confident about charging their phones.
OnePlus "encrypted" batteries
The OnePlus Pad has a serialized battery, meaning the device detects repairs not approved by OnePlus, which can result in functionality being disabled. This is an anti-repair practice first seen on Apple iPhone 11.
OnePlus used the term "encryption" to describe this battery serialization. Critics noted that "encryption" carries positive associations unrelated to its use here, and that the term obscures the restriction's effect on independent repair.[6][7]
"Web Environment Integrity API" by Google
Google tried to implement Digital Rights Management (DRM) on the Internet, giving it the name "Web Environment Integrity API".[8][9]
"To enhance our services"
Samsung "offers additional content" by advertising on refrigerators
This is an update message shown on a Samsung refrigerator:
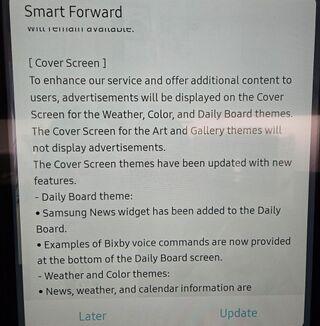
To enhance our service and offer additional content to users, advertisements will be displayed [...]
Despite using benevolent-seeming phrases such as "enhance our service" and " offer additional content", the update introduced advertisements on the refrigerator's display.[5]
"To streamline the experience"
Fewer ports on modern laptops
In the 2000s and early 2010s, three or four USB ports built into laptops were not uncommon. Modern laptops in contrast usually feature one or two USB-A ports and might feature an USB-C port, in addition to less modular and less upgradeable parts. In reality, this has the opposite effect: due to fewer built-in ports on their laptops, the user is forced to carry hubs and adapters to be able to use the same functionality as before, which outweighs any portability benefit that the thinness might have afforded. Netbooks already existed as the category of laptops for people primarily interested in thinness.[10]
Google wants to help cleaning up MicroSD cards by denying normal write access
MicroSD cards became a major selling point of Android smartphones compared to iPhones, allowing the expansion of the storage capacity by multiple times at a time where smartphone internal storage capacities were only in the double-digit gigabytes. In addition, MicroSD cards make it easy to rescue data from a broken smartphone and to get immediate free storage within minutes without hour-long file transfers.
In Android 4.4 KitKat, Google revoked normal write access to the MicroSD card through applications installed by the user, with the exception of folders dedicated to each app at "Android/data/(package name)". The write access could not be restored through a setting in the menu, only through rooting.
Google's argument was to ensure no app can leave files behind after uninstallation:
The WRITE_EXTERNAL_STORAGE permission must only grant write access to the primary external storage on a device. Apps must not be allowed to write to secondary external storage devices, except in their package-specific directories as allowed by synthesized permissions. Restricting writes in this way ensures the system can clean up files when applications are uninstalled.
Google restored write access in Android 5.0 through the Storage Access Framework. However, the framework introduces processing overhead that reduces speeds, particularly when handling large numbers of files.[3][4]
References
- ↑ Temelkov, Ilia (2025-08-25). "Google will make sideloading apps way more difficult from next year". PhoneArea. Archived from the original on 15 Nov 2025. Retrieved 2025-10-01.
- ↑ Sohn, Jiyoung (2026-03-23). "Ads Are Popping Up on the Fridge and It Isn't Going Over Well". The Wall Street Journal. Archived from the original on 2026-03-23. Retrieved 2026-04-09.
{{cite web}}:|archive-date=/|archive-url=timestamp mismatch; 2026-03-26 suggested (help) - ↑ 3.0 3.1 The Storage Access Framework is the only way for apps to work with all your files in Android Q. And it's terrible. - XDA developers (Archived)
- ↑ 4.0 4.1 "Horrible access storage framework performance". Reddit - r/androiddev. 14 Apr 2017. Archived from the original on 23 Aug 2025.
- ↑ 5.0 5.1 Samsung Galaxy Unpacked 2015 - Livestream (Replay (Archived)
- ↑ Rossmann, Louis (2023-02-08). "Oneplus' tablet uses an encrypted battery; how's that for repairability?". YouTube (Video). Archived from the original on 16 Feb 2026. Retrieved 2025-10-01.
- ↑ Amadeo, Ron (2023-02-07). "OnePlus takes on the iPad with the OnePlus Pad". Ars Technica. Archived from the original on 18 Nov 2025. Retrieved 2025-10-01.
- ↑ Google's trying to DRM the internet, and we have to make sure they fail - Louis Rossmann (Brighteon mirror, BitChute mirror) (Archived)
- ↑ Bruchon, Jody (2023-07-22). "Web Environment Integrity Must Be Stopped: Enslavement By "Remote Attestation"". jodybruchon.com. Archived from the original on 1 Dec 2025. Retrieved 2025-10-01.
- ↑ Victor (2022-11-24). "Why are so many laptops having less ports?". easydongle.com. Archived from the original on 18 Nov 2025. Retrieved 2025-10-02.
